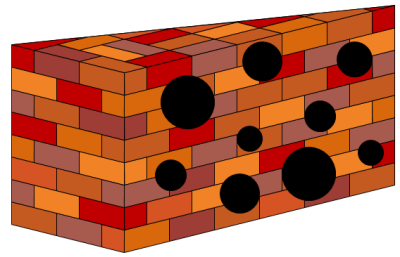
Firewalls can be difficult to manage. Often times rules lack granularity due to a lack of understanding of the application traffic or trying to keep up with the speed of business. Firewalls get more and more rules added to their policies to the point of becoming "Swiss cheese". Don't give up hope because there are methods and tools available to help you gain control of your firewall policies.
A firewall simply implements the security policy of an organization. It is pointless to implement a firewall without strong policies defining traffic types that are permitted or denied. Good firewall design policy specifies the rules used to implement the minimum permissions required to allow the application to function. This policy must be designed with the capabilities and weaknesses of firewall and the application in mind. Typically firewall policies are based on one of two strategies. Either they permit any service unless it is expressly denied or they deny all services unless expressly allowed. The later is the preferred industry best practice fail-safe stance. However, during security assessments, we still find firewall policies where the first rule is "permit ip any any".
No comments:
Post a Comment